Tag router
This website is hosted on my own dedicated server (a kimsufi) and like every server, it’s getting regularly attacked. To identify those attacks, I needed to add a layer of security to ban recurrent attempt, this layer is Fail2ban. It’s… Continue Reading →
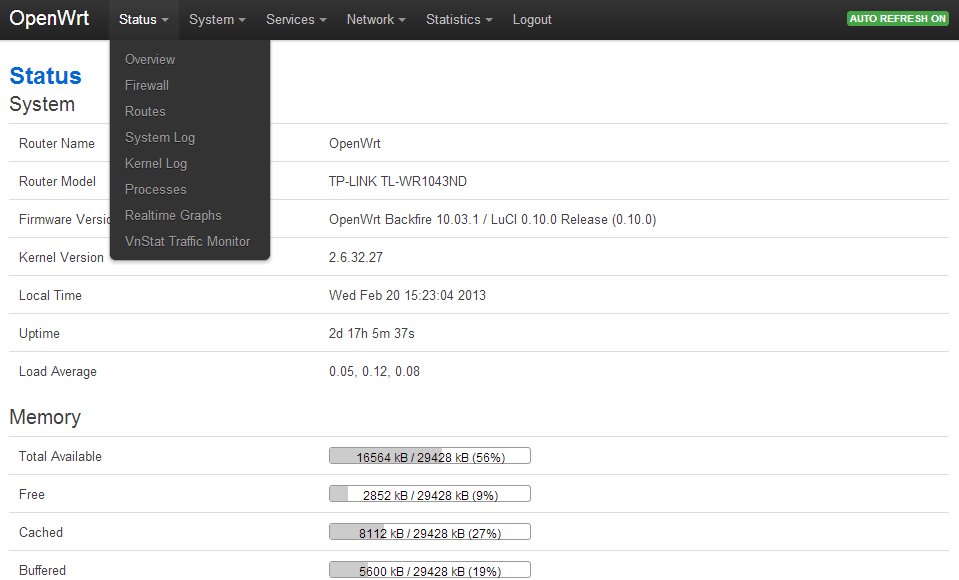
Introduction I was using the Raspberry Pi as my wifi router, but I have to admit I reached it’s limit quite soon. Even with a good wifi usb dongle, I couldn’t get a stable and fast connection. I then bought… Continue Reading →